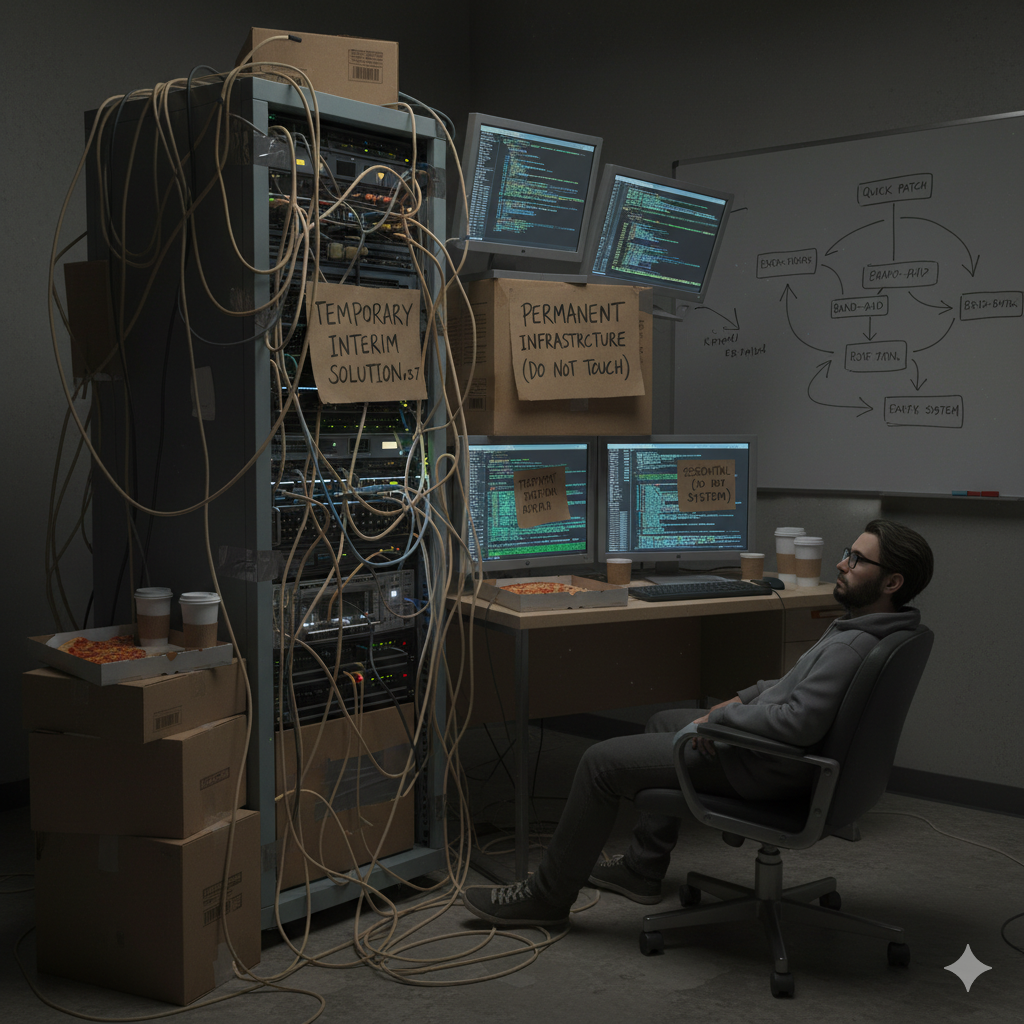
In fast-moving business environments, temporary solutions often feel necessary. A quick patch to stabilize a system, a short-term integration to connect two platforms, or a manual workaround to meet a deadline can appear practical and efficient. In moments of urgency, implementing a rapid solution inside the enterprise IT infrastructure seems responsible. After all, the goal is continuity. However, what begins as a short-term adjustment frequently evolves into a long-term dependency. Over time, these provisional measures embed themselves into the enterprise technology stack, quietly shaping operations, security, and scalability in ways never intended.
Temporary fixes are rarely designed with long-term performance, scalability, or compliance in mind. They are built to solve immediate friction inside the digital operations framework. Yet once implemented, priorities shift. New projects emerge, leadership focuses on growth, and the “temporary” solution continues functioning just well enough to avoid urgent replacement. Months pass. Sometimes years. Eventually, the workaround becomes normalized within the business technology ecosystem, and its provisional nature is forgotten.
The risk lies not in the initial fix, but in the absence of structured follow-up within the enterprise IT governance framework. Without clear timelines for review and replacement, stopgap measures accumulate. Scripts written to bridge integration gaps remain active long after proper integration tools become available. Manual approval chains substitute for automated workflows within the enterprise workflow management system. Legacy hardware continues supporting expanding workloads because it still technically operates. Each instance reinforces a pattern: urgency overrides architecture.
As organizations grow, these accumulated workarounds form an invisible layer of complexity within the enterprise application environment. What appears stable on the surface is often supported by fragile, undocumented adjustments beneath. For example, a temporary database patch designed to accommodate increased reporting demands may persist without optimization. Over time, performance degradation becomes noticeable inside the enterprise data management framework, yet the root cause traces back to an old workaround no longer remembered as temporary.
One of the most significant consequences of prolonged temporary fixes is the silent expansion of technical debt accumulation. Technical debt grows when organizations prioritize speed over structured design inside the enterprise architecture strategy. While debt is manageable when acknowledged and tracked, unmonitored accumulation creates compounding risk. Every quick script, manual override, and undocumented integration adds weight to the infrastructure. Eventually, the cost of maintaining these patches surpasses the cost of implementing a permanent solution.
Security exposure also increases when temporary adjustments become permanent fixtures within the enterprise cybersecurity architecture. Rapid fixes often bypass comprehensive testing and may not align with established controls in the digital risk management framework. A short-term firewall exception, a shared administrative credential, or a bypassed authentication rule can linger for years. As threat landscapes evolve, these legacy exceptions create exploitable vulnerabilities. Because they were originally introduced during urgent situations, they are rarely revisited during routine audits of the enterprise security governance model.
Operational efficiency gradually erodes as well. Manual processes introduced to compensate for missing automation inside the digital productivity ecosystem become ingrained in daily routines. Employees adjust, creating spreadsheets, email approvals, and duplicate entries to bridge system limitations. Over time, these practices weaken consistency within the enterprise IT operations structure. Productivity declines incrementally, not dramatically, making inefficiencies difficult to quantify. What began as a temporary workaround to meet a deadline transforms into a permanent drag on performance.
Another overlooked impact is scalability restriction. Temporary fixes are not engineered to support growth within the enterprise infrastructure lifecycle. As transaction volumes increase and data complexity expands, fragile patches struggle to keep pace. Performance bottlenecks appear inside the cloud computing environment or on-premise servers. Instead of addressing root architecture gaps, organizations often add additional patches. This layering effect compounds complexity inside the broader enterprise technology governance model, reducing resilience.
Documentation gaps further compound risk. Temporary solutions are frequently implemented without thorough recording in the enterprise knowledge management system. When the original architect leaves or transitions roles, understanding of those modifications fades. Successor teams inherit systems supported by undocumented scripts and customizations embedded in the enterprise application ecosystem. Troubleshooting becomes investigative work. Time is spent reverse-engineering decisions rather than advancing strategic initiatives within the digital transformation roadmap.
Financial implications are equally significant. While temporary fixes may appear cost-effective initially, long-term maintenance costs accumulate within the enterprise financial governance framework. Continuous monitoring, manual reconciliation, and reactive troubleshooting consume labour hours. Emergency interventions triggered by fragile integrations introduce unpredictable expenditures. Organizations often underestimate the total cost of ownership associated with sustained reliance on provisional infrastructure inside the business technology ecosystem.
Temporary fixes also shape organizational culture. When quick patches consistently replace long-term planning, teams internalize urgency as the default operating mode. Strategic architecture discussions inside the enterprise IT strategy alignment process are postponed in favour of immediate stabilization. Over time, innovation slows. Instead of investing in scalable automation within the digital innovation framework, teams focus on maintaining fragile systems. The culture shifts from proactive development to reactive survival.
Leadership visibility can also be compromised. Temporary reporting adjustments within the enterprise business intelligence system may distort data accuracy. Manual exports and stitched-together dashboards introduce inconsistencies in the enterprise data governance model. Executives relying on these metrics may make strategic decisions based on incomplete or misaligned information. The longer provisional reporting solutions remain active, the greater the risk of misinformed planning.
Compliance exposure increases when stopgap measures bypass structured oversight inside the enterprise compliance management framework. Regulatory standards often require consistent controls, documented processes, and validated configurations. Temporary adjustments implemented during urgent situations may not undergo compliance review. As regulations evolve, legacy workarounds inside the enterprise IT audit structure create gaps that surface only during external inspections.
Vendor relationships may also suffer. Custom scripts and integrations layered onto third-party systems within the enterprise technology vendor management strategy complicate support agreements. Vendors may decline assistance for heavily modified environments. Upgrades become difficult because customizations conflict with new releases. Organizations find themselves locked into outdated versions of the enterprise software infrastructure, unable to modernize without extensive reconfiguration.
The psychological comfort of “it still works” reinforces inaction. As long as systems remain functional, leadership may deprioritize replacement. However, stability built on fragile foundations is deceptive. The absence of immediate failure does not indicate structural strength within the enterprise IT resilience model. Rather, it often masks vulnerability waiting for a triggering event rapid growth, cyberattack, regulatory change, or hardware failure.
Addressing this issue requires structured intervention. Organizations must conduct periodic reviews of all temporary implementations inside the enterprise architecture governance framework. Each workaround should be evaluated for relevance, risk, and scalability. Clear sunset policies within the IT lifecycle management strategy ensure that temporary measures have defined expiration timelines. Documentation standards inside the enterprise knowledge governance system should mandate recording of all modifications, regardless of urgency.
Cross-functional oversight strengthens accountability. When decisions affecting the enterprise technology ecosystem involve multiple stakeholders IT, finance, compliance, operations the likelihood of permanent provisional infrastructure decreases. Collaborative planning embedded in the digital transformation governance structure ensures that speed does not permanently override design.
Investment discipline is equally important. Allocating budget specifically for modernization inside the enterprise technology investment framework prevents indefinite reliance on temporary measures. Organizations should treat infrastructure improvements not as discretionary expenses but as strategic imperatives aligned with growth objectives.
Technology inevitably evolves. Systems that once required temporary patches may now have scalable solutions available within the cloud-based enterprise platform environment. Regular reassessment ensures that outdated workarounds are replaced with resilient alternatives. Proactive replacement strengthens stability within the enterprise infrastructure lifecycle management process.
Ultimately, temporary fixes are not inherently problematic. They are often necessary responses to urgent challenges. The true risk emerges when urgency becomes permanence. When provisional adjustments quietly transform into foundational infrastructure, organizations inherit fragility disguised as functionality. Sustainable growth requires deliberate architecture, disciplined governance, and transparent documentation within the broader business technology strategy.
By identifying, auditing, and systematically replacing outdated stopgaps, organizations reclaim control over their enterprise IT landscape. Infrastructure should be designed intentionally, not accidentally. When temporary solutions are acknowledged as temporary and managed accordingly they serve their purpose without compromising long-term resilience. The difference between agility and instability lies in whether short-term fixes remain controlled exceptions or evolve into unintended foundations within the enterprise technology framework.